How to Protect your PC from Ransomware Cryptolocker

Ransomware is malicious software that cyber criminals use to hold your computer or computer files for ransom, demanding payment from you to get them back. Sadly, ransomware is becoming an increasingly popular way for malware authors to extort money from companies and consumers alike.
There is a variety of ransomware can get onto a person’s machine, but as always, those techniques either boil down to social engineering tactics or using software vulnerabilities to silently install on a victim’s machine.
About Cryptolocker :
Cryptolocker ransomware threat that has been in the news a lot lately .
The perpetrators of Cryptolocker have been emailing it to huge numbers of people. Like a notorious criminal, this malware has been associated with a variety of other bad viruses – backdoor Trojans, downloaders, spammers, password-stealers, ad-clickers and the like.
Cryptolocker may email or by way of a backdoor or downloader, brought along as an additional component.Initially emails were targeting home users, then small to medium businesses, and now they are going for enterprises as well. The malware also spreads via RDP ports that have been left open to the Internet, as well as by email.
Cryptolocker can also affect a user’s files that are on drives that are “mapped”, which is to say, they have been given a drive letter (e.g. D:, E:, F: ).This could be an external hard-drive including USB thumb drives, or it could be a folder on the network.
At this point, 1% of machines have been affected, though it is estimated that the criminals have sent millions of emails. Hopefully the remainder of recipients simply deleted the malicious emails without opening them, rather than them sitting unopened, waiting to unleash more pain.
Those people that have been affected have had a large number of their files encrypted. These files are primarily popular data formats, files you would open with a program (like Microsoft Office, Adobe programs, iTunes or other music players, or photo viewers).
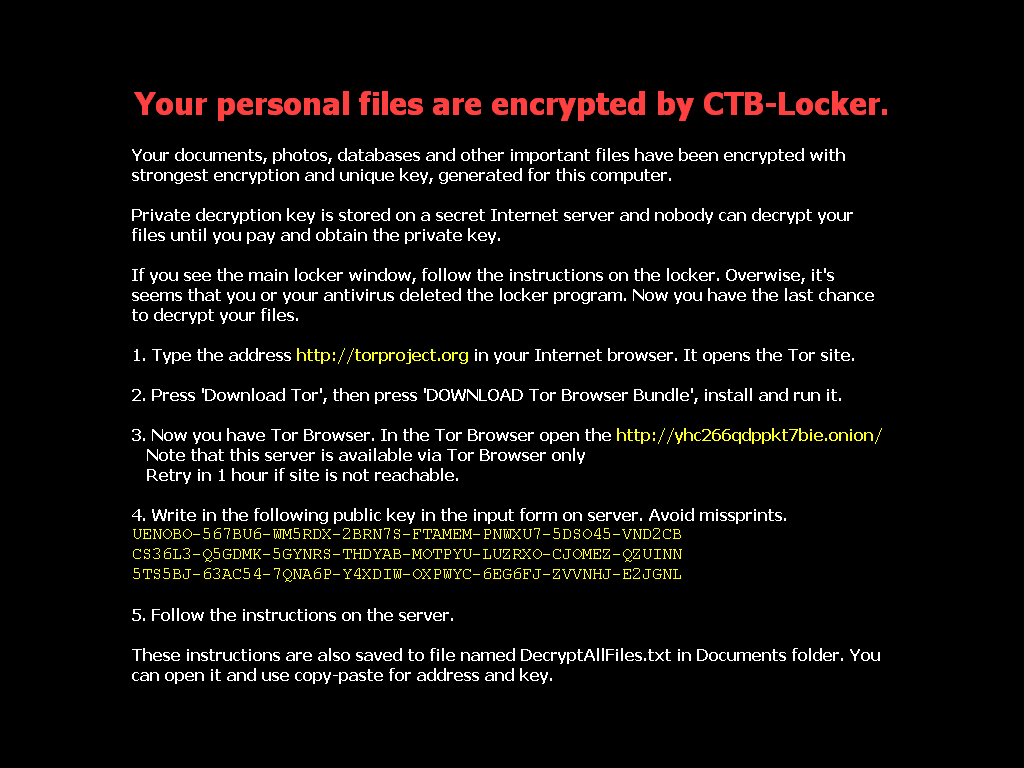
The malware authors use two types of encryption: The files themselves are protected with 256-bit AES encryption. The keys generated by this first encryption process are then protected with 2048-bit RSA encryption, and the malware author keeps the private key that would allow both the keys on the user’s machine and the files they protect, to be decrypted. The decryption key cannot be brute-forced, or gathered from the affected computer’s memory. The criminals are the only ones who ostensibly have the private key.
What can you do about it?
Here are a few tips that will help you keep ransomware from wrecking your day:
1. Back up your data using automatic and in-built Net Protector Databackup Software
(View our Article on NP Data Backup)
Backup documents. Users should do well to back up their documents. The single biggest thing that will defeat ransomware is having a regularly updated backup. If you are attacked with ransomware you may lose that document, but if you can restore your system to an earlier snapshot or clean up your machine and restore your other lost documents from backup, you can rest easy.
Remember that Cryptolocker will also encrypt files on drives that are mapped. This includes any external drives such as a USB thumb drive, as well as any network or cloud file stores that you have assigned a drive letter. So, what you need is a regular backup regimen, to an external drive or backup service, one that is not assigned a drive letter or is disconnected when it is not doing backup.
2. Show hidden file-extensions
One way that Cryptolocker frequently arrives is in a file that is named with the extension “.PDF.EXE”, counting on Window’s default behavior of hiding known file-extensions. If you re-enable the ability to see the full file-extension, it can be easier to spot suspicious files.
3. Filter EXEs in email
Scrutinize email messages carefully. Be wary of every email you receive, specially those from unverified sources.
you may deny mails sent with “.EXE” files, or to deny mails sent with files that have two file extensions, the last one being executable (“*.*.EXE” files, in filter-speak).
Refrain from clicking links embedded in email. It is best to avoid clicking links in email.
If you do need to exchange executable files over mail, you can do so with ZIP files (password-protected, of course) or via cloud services.
4. Disable files running from AppData/LocalAppData folders
You can create rules within Windows or with Intrusion Prevention Software, to disallow a particular, notable behavior used by Cryptolocker, which is to run its executable from the App Data or Local App Data folders.
Net Protector is updated regularly as we discover new techniques used by new versions of Cryptolocker.
5. Disable RDP
The Cryptolocker/Filecoder malware often accesses target machines using Remote Desktop Protocol (RDP), a Windows utility that allows others to access your desktop remotely. If you do not require the use of RDP, you can disable RDP to protect your machine from Filecoder and other RDP exploits. For instructions to do so, visit the appropriate Microsoft Knowledge Base article.
6. Use a reputable security suite like Net Protector Total Security having all features like Firewall and Anti-Malware
It is always a good idea to have both anti-malware software and a software firewall to help you identify threats or suspicious behavior. Malware authors frequently send out new variants, to try to avoid detection, so this is why it is important to have both layers of protection. And at this point, most malware relies on remote instructions to carry out their misdeeds. If you run across a ransomware variant that is so new that it gets past anti-malware software, it may still be caught by a firewall when it attempts to connect with its Command and Control (C&C) server to receive instructions for encrypting your files.
Though no known CryptoLocker and ransomware were found to exploit any software vulnerabilities, it is best to update your Antivirus software with the latest tools and databases. This provides added layer of protection against online threats in general.
If you find yourself in a position where you have already run a ransomware file without having performed any of the previous precautions, your options are quite a bit more limited. But all may not be lost.
There are a few things you can do that might help mitigate the damage, particularly if the ransomware in question is Cryptolocker:
1. Disconnect from WiFi or unplug from the network immediately
If you run a file that you suspect may be ransomware, but you have not yet seen the characteristic ransomware screen, if you act very quickly you might be able to stop communication with the C&C server before it finish encrypting your files. If you disconnect yourself from the network immediately (have I stressed enough that this must be done right away?), you might mitigate the damage. It takes some time to encrypt all your files, so you may be able to stop it before it succeeds in garbling them all. This technique is definitely not foolproof, and you might not be sufficiently lucky or be able to move more quickly than the malware, but disconnecting from the network may be better than doing nothing.
2. Use System Restore to get back to a known-clean state
If you have System Restore enabled on your Windows machine, you might be able to take your system back to a known-clean state. But, again, you have to out-smart the malware. Newer versions of Cryptolocker can have the ability to delete “Shadow” files from System Restore, which means those files will not be there when you try to to replace your malware-damaged versions. Cryptolocker will start the deletion process whenever an executable file is run, so you will need to move very quickly as executables may be started as part of an automated process. That is to say, executable files may be run without you knowing, as a normal part of your Windows system’s operation.
3. Use Net Protector Data Backup feature to Restore your important Data Files
we strongly advise that you do not pay the ransom. Paying the criminals may get your data back, but there have been plenty of cases where the decryption key never arrived or where it failed to properly decrypt the files and it encourages criminal behavior






