Malware Alerts
-
Read moreA supply chain attack called Mini Shai-Hulud compromised multiple npm packages in the @antv ecosystem, injecting credential-stealing malware. Developers using affected packages risk stolen tokens, data exfiltration, and persistent malware infections.
-
Read moreCybersecurity researchers have discovered fake GitHub repositories impersonating DeepSeek TUI to deliver malware. The campaign uses compressed archives and multi-stage payloads to bypass detection, disable Windows Defender, and establish persistent access on infected systems.
-
Read moreHackers are using fake Claude AI installer pages and Google Ads to spread malware, steal credentials, and infect Windows and macOS systems.
-
Read moreHackers compromised official DAEMON Tools installers with malware in a major supply chain attack affecting users worldwide. Learn how to stay protected.
-
Read moreHackers exploit Google Ads to steal cryptocurrency using fake sites, wallet drainers, and seed phrase phishing, causing major financial losses in 2026.
-
Posted: April 22, 2026Views: 36Read moreNew LOTUSLITE malware linked to Mustang Panda targets India’s banking sector and South Korean policy groups in advanced cyber-espionage attacks.
-
Read moreCybercriminals abuse n8n AI workflow automation to deliver malware through trusted webhooks, bypassing security filters and targeting enterprise users.
-
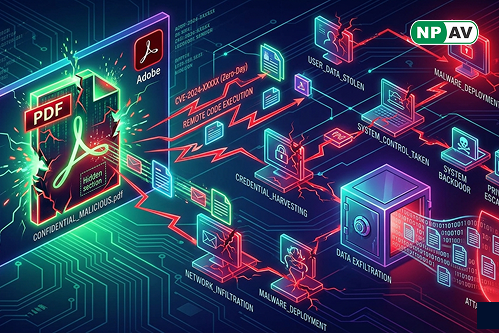
Read moreAdobe Acrobat Reader zero-day vulnerability exploited through malicious PDFs to steal data and gain system access. Learn risks and protection tips.
-
Read moreHackers use fake antivirus software to deliver LucidRook malware in targeted attacks on Taiwan NGOs and universities, exploiting spearphishing techniques.
-
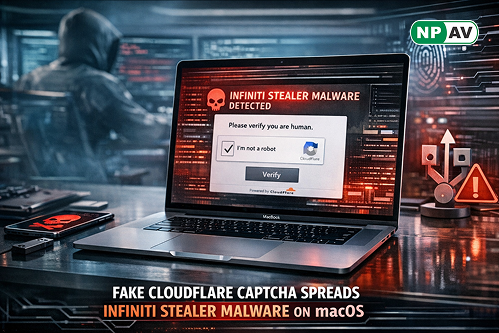
Read moreInfiniti Stealer is a new macOS malware spreading through fake Cloudflare CAPTCHA pages, tricking users into running malicious commands and stealing sensitive data.