fp-2c
-
Read moreCybercriminals abuse n8n AI workflow automation to deliver malware through trusted webhooks, bypassing security filters and targeting enterprise users.
-
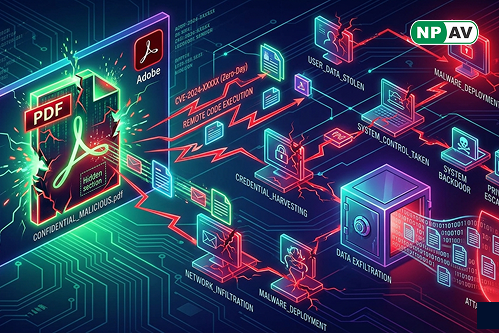
Read moreAdobe Acrobat Reader zero-day vulnerability exploited through malicious PDFs to steal data and gain system access. Learn risks and protection tips.
-
Read moreA critical React Server Components flaw (CVE-2026-23869) allows attackers to trigger DoS attacks by exhausting server resources with crafted requests.
-
Read moreHackers abuse Meta Business Manager notifications to send phishing emails from trusted domains, targeting businesses and stealing login credentials.
-
Posted: April 08, 2026Views: 38Read moreIndian Bank alerts users about fake LPG payment and KYC scams spreading via WhatsApp and SMS to steal banking details and commit fraud.
-
Posted: April 06, 2026Views: 149Read moreDelhi Police busts ₹300 crore cyber fraud syndicate linked to fake investment apps, arrests mastermind and uncovers global scam network.
-
Posted: April 01, 2026Views: 107Read moreHackers exploit hotel booking systems to send fake payment requests via WhatsApp and email, using real reservation data to scam travelers worldwide.
-
Posted: March 25, 2026Views: 70Read moreA phishing campaign uses fake resume files to infect enterprise systems with credential stealers and crypto miners, targeting corporate networks with advanced malware.
-
Read moreFBI and CISA warn of Russian-linked phishing attacks targeting WhatsApp and Signal users to steal accounts using fake support messages and verification code scams.
-
Read moreApple warns that outdated iPhones are vulnerable to Coruna and DarkSword exploit kits. Users are urged to update iOS or enable Lockdown Mode to stay protected.