TeslaCrypt 3.0 Released with .XXX, .TTT, and .MICRO File Extensions

A new version of the TeslaCrypt Ransomware version 3.0, uses a different encryption key exchange algorithm. All encrypted files will now have the new .XXX, .TTT, .MICRO extensions appended to them.
The major and most problematic change, though, is key exchange being modified. In the past there were ways to recover the private key from an encrypted file. Now with this modification, this is longer possible for new victims.
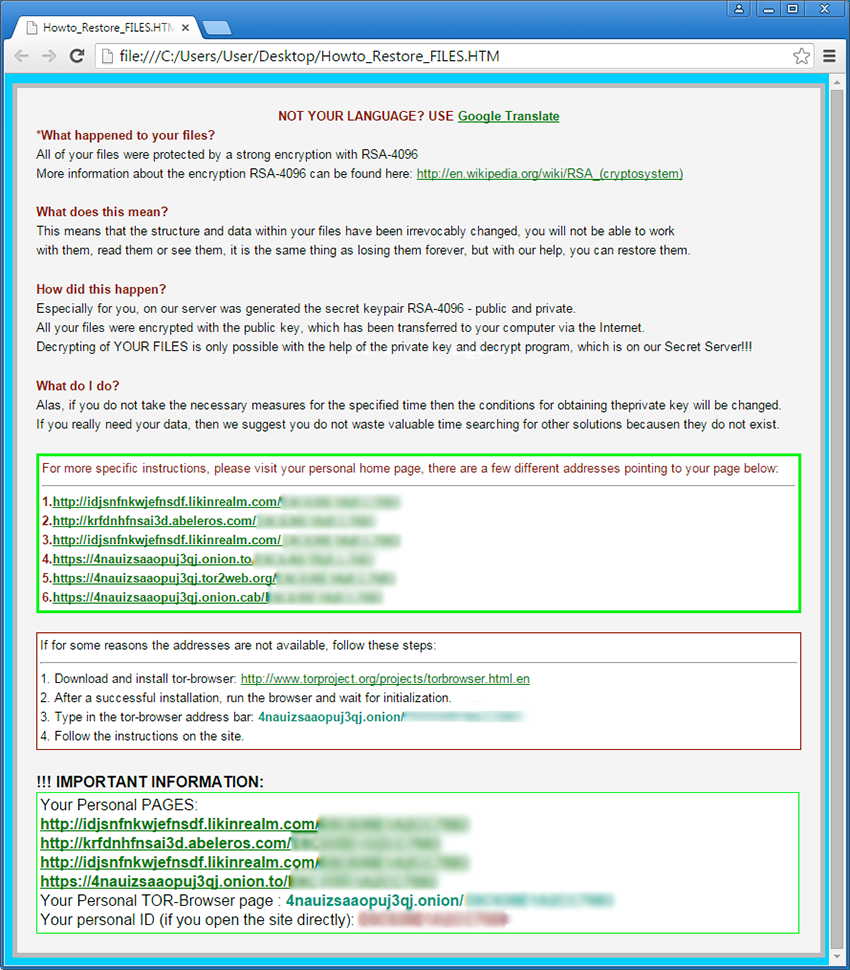
The infection brings up a ransom notification in a file named Howto_Restore_FILES.HTM (.BMP / .TXT) that says “All of your files were protected by a strong encryption with RSA-4096 and pay a ransom of about 500 USD”.
All Users are requested to:
- Install and keep NPAV updated up-to-date.
- Make sure NPAV Data Backup is ON.
- Always use trusted and secure sites for downloading setups.
Net Protector customers are protected from such new and dangerous ransomware.
Comment(s)