Blogs
-
Read more
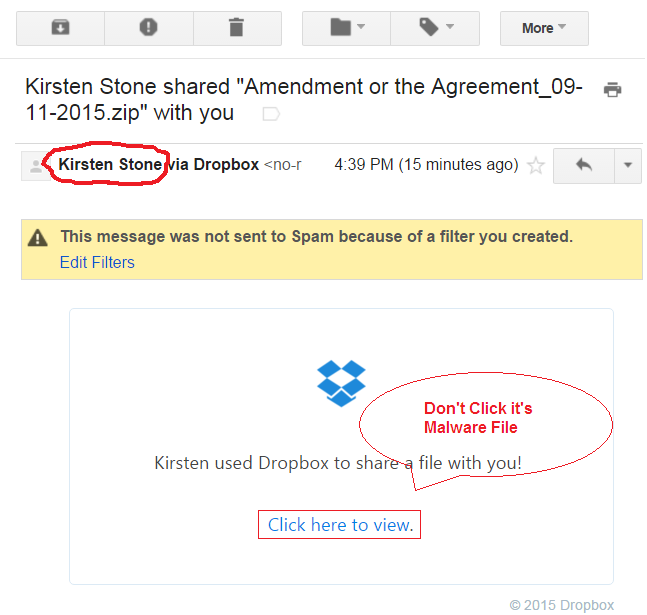
Hackers have launched a global spear-phishing campaign to target several organizations.
Read moreVarious established and famous android apps are still operating over unpatched modules.
Read moreIIMJobs is one of the leading and one of the 700 most visited sites in India.
Read moreA retooled version of 13 years old malware is being used by hackers to target multiple sectors.
Read moreBruteforcing attacks have allowed hackers to bypass 2FA of WHM and cPanel.
Posted: November 23, 2020Views: 106Read moreHackers were found exploiting a new bug detected in Facebook Messenger.
Read moreA new phishing email requesting user password confirmation was found in user inboxes.
Read moreAndroid app with over 100 million downloads found exposing messages.
Read moreHackers have leaked an entire database containing login data of 100k Facebook users.
Read moreNew information stealer malware dubbed as Jupyter is targeting web browser data.
Read moreThis Diwali, enjoy cybersecurity at never seen before prizes with NPAV's outstanding offers.
Posted: November 12, 2020Views: 95Read moreMultiple firms have been targeted by Ragnar Locker ransomware by using Facebook ads.
Posted: November 11, 2020Views: 83Read moreA Brazillian threat group has launched Ghimob banking trojan in multiple countries.
Read moreIndia's biggest online supermarket "BigBasket" has recently suffered a massive data breach.
Read moreNPAV researchers have reported an all-new malware campaign stealing login credentials.
Read moreHackers are using outgoing calls made by users for generating profit.
Read moreResearchers have found new ransomware being spread by hackers using phishing emails.
Posted: November 02, 2020Views: 86Read moreGoogle's researchers have given all the details related to the vulnerability impacting Windows 7 and 10.
Back to Top