Kimsuky Hackers Use Custom RDP Wrapper for Stealthy Remote Access

North Korean hacking group Kimsuky is using a custom RDP Wrapper and proxy tools to gain persistent, stealthy access to infected computers. This marks a shift in their tactics, moving away from noisy malware to more covert remote access techniques.
- Kimsuky hackers use spear-phishing emails with malicious .LNK file attachments disguised as PDFs or Word documents.
- The infection process begins when the victim opens the .LNK file, triggering PowerShell or Mshta to download additional malware payloads.
- A modified RDP Wrapper tool is installed, allowing persistent and undetected Remote Desktop Protocol (RDP) access.
- Attackers deploy proxy tools to bypass network restrictions and ensure uninterrupted access even when direct RDP connections are blocked.
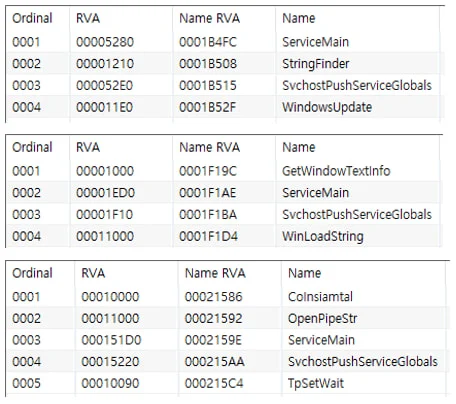
- Secondary payloads include:
- Keyloggers to record keystrokes and steal sensitive information.
- Infostealer (forceCopy) to extract saved credentials from web browsers.
- PowerShell-based ReflectiveLoader for executing malware in memory, evading detection. - The custom RDP Wrapper evades antivirus detection, making Kimsuky’s presence harder to trace.
- The attack allows long-term surveillance, helping Kimsuky conduct cyber-espionage and intelligence gathering.
Kimsuky’s evolving tactics show how cyber threats are becoming more sophisticated and stealthy. Businesses must strengthen email security, endpoint protection, and network monitoring to detect such attacks early. Net Protector Cyber Security (NPAV) provides advanced threat detection and RDP attack prevention to safeguard against such cyber-espionage threats.
Comment(s)