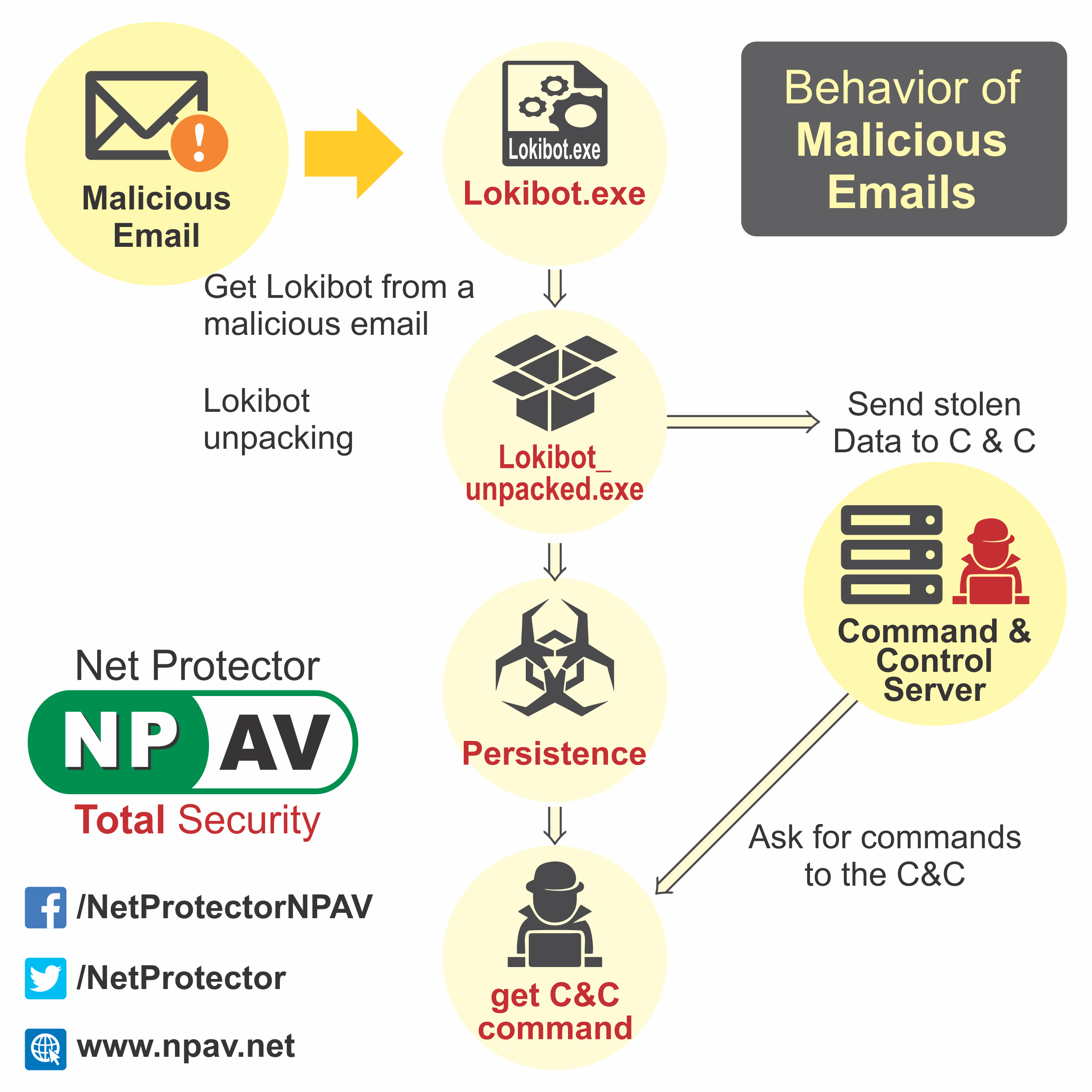
Loki bot malware stealing victim passwords from browsers, messaging applications, email and ftp clients
NPAV Cybersecurity Labs has researched and discovered that hackers are spreading malware which can steal users passwords from various applications.
Lokibot belongs to such malware family. Lokibot malware steals data from emails, Browsers and Ftp by spreading as .iso extension file that target a corporate network and applications to steal victim credentials.
How is the lokibot malware spreading?
Attackers have been spreading the malicious file via email that contains malicious “.iso” attachment. Once the user clicks on the .iso attachment, the malware file inside .iso file is extracted.
Loki Bot Malware also capable of stealing wallets and share the stolen data with attackers via its C&C server.
According to NPAV observations and research new malware and continuously evolving and improving their attack platforms.
NPAV Total Security protects users from such new malware threats.
2 Comment(s)
Abhijit
Dec 20, 2018 18:59
Best . Nice
DGhate
Dec 18, 2018 22:49
Nice Blog...