Steganographic Cyberattack Uses JPG Images to Spread Dangerous Malware

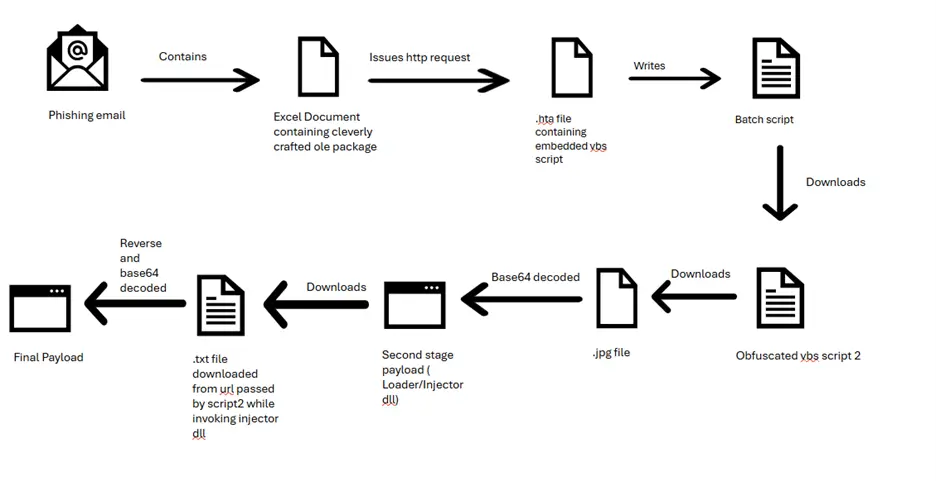
Cybercriminals have developed a new malware attack that hides harmful software inside JPEG image files, allowing them to steal passwords from unsuspecting victims. By using steganography, a technique that hides data inside images, hackers can bypass security defenses and infect devices.
How This Attack Works
Researchers have found that attackers are embedding malicious code into seemingly harmless JPG image files. Once the infected image is downloaded or viewed, hidden scripts inside the file automatically execute, installing password-stealing malware without the user’s knowledge.
- Stealthy Malware Delivery
The attack method allows malware to hide inside image files, making it difficult for antivirus software to detect. - Targets Sensitive User Data
The malware steals passwords from browsers, email clients, and FTP applications, compromising personal and business accounts. - Uses Advanced Steganography
Unlike traditional malware, the malicious code is hidden in pixel data fields rather than metadata, making it almost invisible to detection tools. - Multiple Malware Variants Delivered
The attack installs well-known password-stealing malware such as Vidar, Raccoon, and Redline, which send stolen data to hacker-controlled servers. - Custom Decoding Techniques
Attackers use Python and C++ scripts to extract malware from infected images. These scripts scan specific pixels in the image, rebuild the hidden code, and trigger the infection process.
This sophisticated steganographic attack shows how cybercriminals are finding new ways to bypass security defenses. To stay protected, users and businesses must be cautious when downloading images, avoid opening files from unknown sources, and use advanced security solutions like Net Protector to detect hidden threats. Proactive cybersecurity measures are crucial in defending against evolving malware attacks.