TsarBot Android Malware Targets 750+ Banking & Finance Apps

A dangerous Android banking malware named TsarBot is spreading rapidly, targeting over 750 banking, finance, cryptocurrency, and e-commerce apps worldwide. It uses fake login screens, phishing sites, and remote control techniques to steal user credentials and execute fraudulent transactions.
- Targets Global Banking & Finance Apps – Affects banking, crypto, and e-commerce platforms across multiple regions.
- Disguised as Google Play Services – Users unknowingly install malware from phishing sites posing as legitimate services.
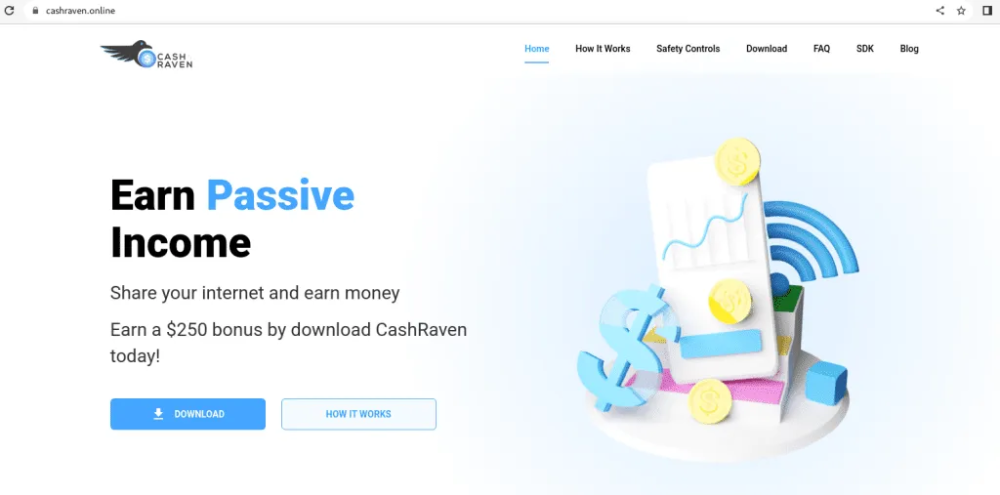
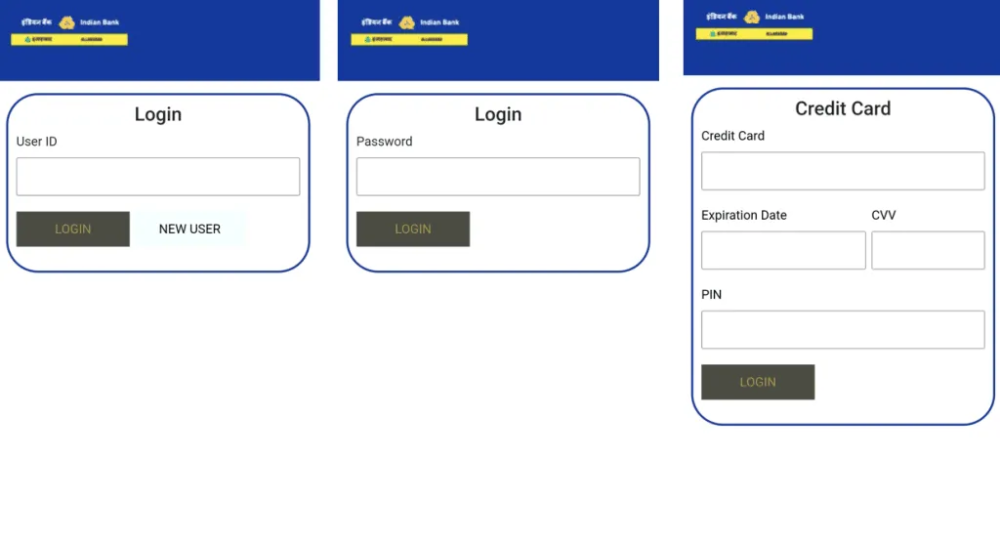
- Overlay Attacks for Credential Theft – Fake login pages trick users into entering banking details, passwords, and credit card information.
- Remote Control via C&C Server – Attackers use WebSocket protocols to control infected devices, mimicking real user activity.
- Steals Lock Screen Credentials – Uses fake lock screens to capture PINs and unlock patterns for full device access.
- Records Screens & Intercepts SMS – Exploits Android Accessibility services for deeper access to personal data.
To Protect Yourself
- Download apps only from official sources like Google Play Store.
- Enable Google Play Protect to detect and block malicious apps.
- Never click on suspicious links in emails or SMS messages.
- Use strong passwords and enable multi-factor authentication (MFA) for banking apps.
- Regularly update your Android device and applications to patch security flaws.
TsarBot is a highly advanced mobile banking trojan that combines overlay attacks, phishing, and remote control techniques to steal sensitive data. As mobile malware threats continue to evolve, staying vigilant and adopting strong security practices is crucial to protecting personal and financial information.
Stay safe with NPAV – Your Trusted Cybersecurity Partner!
Comment(s)