Fake Booking Websites Deliver LummaStealer Malware - Beware!

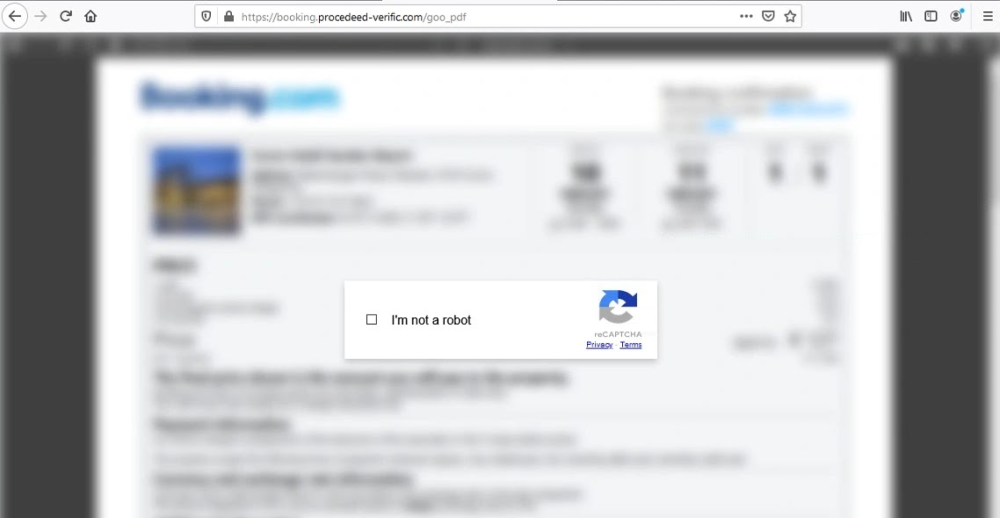
Hackers have launched a new attack using fake hotel and travel booking websites to spread LummaStealer malware. Disguised as legitimate booking confirmation pages, these fraudulent sites trick users into running harmful commands that compromise their personal and financial information.
- Fake Booking Websites – Cybercriminals create phishing sites that look like real travel booking pages.
- Deceptive CAPTCHA Verification – Instead of a real CAPTCHA, users are told to run a command in Windows, which starts the malware infection.
- Targeted Travel Locations – Initially, the scam focused on Palawan, Philippines, but later expanded to Munich, Germany, showing a global attack pattern.
- PowerShell-Based Malware Installation – The malware uses a PowerShell command to bypass security measures and infect systems.
- LummaStealer Malware – Once installed, this malware steals passwords, banking details, and other sensitive information.
- Advanced Evasion Techniques – Attackers use Binary Padding (increasing file size) and Obfuscation (hiding malware in encrypted scripts) to avoid detection.
Hackers are constantly evolving their tactics, and fake booking websites have become a new weapon for spreading malware. The LummaStealer campaign highlights the risks of online travel scams and the importance of cybersecurity awareness.
Stay cautious, verify websites, and never execute unknown commands to keep your data safe!
Comment(s)