Hackers spy on your Computer without you knowing
Posted:
September 10, 2015
Comments:
3
Views:
63
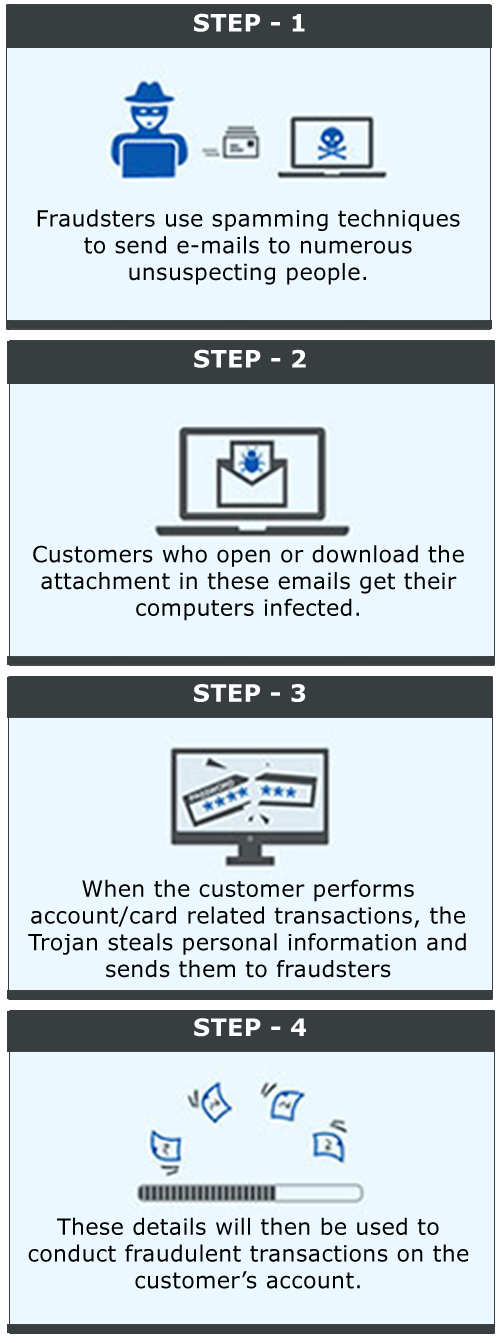
A Trojan is a harmful piece of software that users are typically tricked into downloading and running on their computers. After it is installed and activited, Trojan attacks the computer leading to deletion of files,data theft,or proliferation of viruses.
Trojans can also create back doors to give access to hackers.
How to protect yourself from Fraud :
- Never open e-mails or downlaod attachment from unknown senders. Simply delete such emails
- Install Net Protector Antivirus, it scans every file you download and protect you from malicious files.
- Enable automatic OS updates regularly to keep your Operating System patched against unknown vulnerabilities
- Install patches from software manufacturers as soon as they are distributed. A fully patched computer behind a firewall is the best defense against Trojan.
- Download and use the latest version of your browser.
- If your computer get infected with a Trojan, disconnected your internet connection and remove harmful files with an Net Protector Antivirus Software.
3 Comment(s)
Manendra Prasad sinha
Oct 01, 2015 19:53
Very usefull guidence.Thanks
Prabhakar
Sep 19, 2015 09:22
Thanks for guidance.
dev
Sep 18, 2015 20:04
Thanks for Information...