Unauthorised Unlock Code Blocked

We have found and blocked few unauthorised users of Net Protector.
Some Dealers may be installing Cracked Version of Net Protector on their customer PC. So this has been blocked.
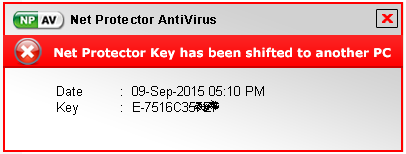
Net Protector Key has been Shifted (Reactived) to another PC
Two Types of Blocking
- Unauthorised or Cracked Keys or Unlock Codes
e.g. :
ZEUV-ENQH-NLTK-PWLK-QPJZ-KKHB
A-15B1A1B4E8 - Key Shifted to Other PC and still using on First PC
This can be done knowingly by customer, or somebody else who has the Key of customer can reactivate on other PC. In this case the first original users NPAV will be Blocked
The followup Popup will be Shown to Customers.
Net Protector Key has been Shifted (Reactived) to another PC
One Key License should be used on one PC Only
Comment(s)
Categories
- Other (43)
- Ransomware (179)
- Events and News (28)
- Features (45)
- Security (505)
- Tips (83)
- Google (49)
- Achievements (13)
- Products (37)
- Activation (7)
- Dealers (1)
- Bank Phishing (61)
- Malware Alerts (301)
- Cyber Attack (385)
- Data Backup (16)
- Data Breach (233)
- Phishing (194)
- Securty Tips (9)
- Browser Hijack (30)
- Adware (15)
- Email And Password (90)
- Android Security (98)
- Knoweldgebase (37)
- Botnet (20)
- Updates (12)
- Alert (72)
- Hacking (90)
- Social Media (11)
- vulnerability (135)
- Hacker (107)
- Spyware (18)
- Windows (31)
- Microsoft (48)
- Uber (1)
- YouTube (4)
- Trojan (7)
- Website hacks (17)
- Paytm (1)
- Credit card scam (4)
- Telegram (9)
- RAT (12)
- Bug (5)
- Twitter (3)
- Facebook (14)
- Banking Trojan (17)
- Mozilla (2)
- COVID-19 (5)
- Instagram (5)
- NPAV Announcement (18)
- IoT Security (4)
- Deals and Offers (2)
- Cloud Security (12)
- Offers (5)
- Gaming (1)
- FireFox (2)
- LinkedIn (3)
- Amazon (5)
- DMart (1)
- Payment Risk (5)
- Occasion (3)
- firewall (5)
- Cloud malware (5)
- Cloud storage (2)
- Financial fraud (115)
- Impersonation phishing (4)
- DDoS (12)
- Smishing (2)
- Whale (0)
- Whale phishing (6)
- WINRAR (3)
- ZIP (2)
- Fraud Protector (101)
-
Mobile Frauds
(80)
- WhatsApp (21)
- AI (42)
- Windows Patch (0)
Recent Posts