Docker CVE-2026-34040 Vulnerability Allows Authorization Bypass and Host Access
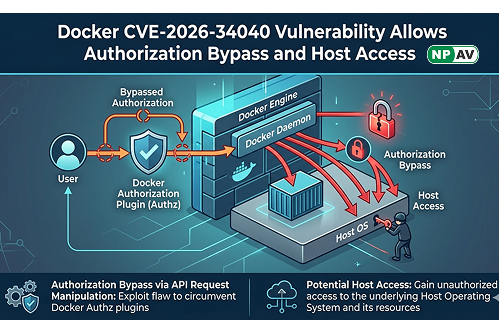
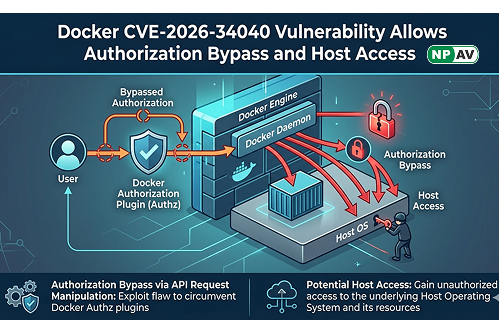
A high-severity vulnerability, CVE-2026-34040, has been discovered in Docker Engine that allows attackers to bypass authorization controls and potentially gain full access to the host system. The flaw is linked to an incomplete fix of a previous issue and can be exploited using specially crafted API requests that prevent authorization plugins from properly inspecting request data.
By sending padded HTTP requests, attackers can trick authorization plugins into approving malicious actions, such as creating privileged containers with root-level access. This can expose sensitive data, including cloud credentials, SSH keys, and Kubernetes configurations, leading to a complete system compromise. The vulnerability affects environments relying on plugins that inspect request bodies for security decisions.
Security experts warn that this flaw could be easily exploited, even by automated tools or AI agents, making it a serious risk for containerized environments. Organizations are advised to update to patched versions, restrict Docker API access, and adopt security practices like rootless mode to minimize impact.
NPAV offers a robust solution to combat cyber fraud. Protect yourself with our top-tier security product, FraudProtector.net