Hackers Use Fake Resumes to Deploy Crypto Miner and Steal Enterprise Credentials

Cybersecurity researchers have uncovered a phishing campaign named FAUX#ELEVATE, where attackers use fake resume files to target enterprise environments and deploy credential stealers along with cryptocurrency miners. The campaign, identified by Securonix, primarily targets French-speaking organizations by sending phishing emails containing heavily obfuscated VBScript files disguised as CV documents.


Once opened, the script displays a fake error message while secretly executing malicious code in the background. It performs evasion checks, prompts users for administrative access, disables security controls like Microsoft Defender, and downloads additional payloads from services like Dropbox. The malware then steals browser credentials, exfiltrates sensitive data, and deploys a Monero cryptocurrency miner, all within seconds of execution.
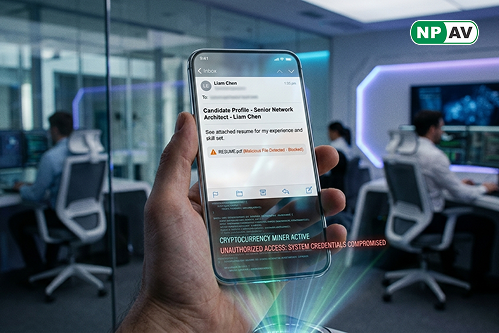
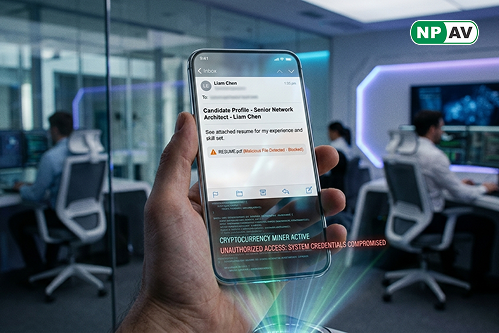
The attack specifically targets enterprise (domain-joined) systems, ensuring maximum value for attackers through corporate credential theft. It uses legitimate tools and infrastructure to stay undetected and cleans up traces after execution, leaving behind only persistent malware components. Security experts warn organizations to remain cautious of unsolicited resume attachments and strengthen email security and endpoint protections.
NPAV offers a robust solution to combat cyber fraud. Protect yourself with our top-tier security product, FraudProtector.net