Malicious PDF exploiting Adobe Acrobat zero-day vulnerability to steal data and compromise systems
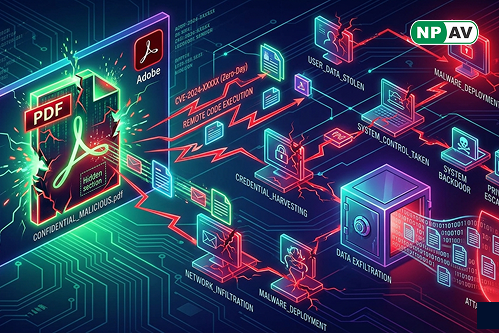
A zero-day vulnerability in Adobe Acrobat Reader is being actively exploited through malicious PDF files to steal sensitive data and potentially take full control of systems. Active since December 2025, the attack requires only opening a PDF, making it highly effective in phishing campaigns.
The exploit abuses built-in Acrobat APIs to access local files and gather system data while adapting its behavior based on the target environment.
Researchers warn that the vulnerability can also enable advanced attacks like remote code execution and sandbox escape, increasing the risk of full system compromise. With no official patch available yet, organizations must rely on strong security practices such as avoiding untrusted PDFs, enabling sandbox protections, and monitoring suspicious activity to reduce exposure.
NPAV offers a robust solution to combat cyber fraud. Protect yourself with our top-tier security product, FraudProtector.net