New FakeCall Malware Hijacks Android Phones to Intercept Banking Calls and Steal Sensitive Data

The latest variant of the FakeCall malware has taken vishing attacks to a new level, hijacking Android devices to intercept banking calls and manipulate call interfaces. This highly sophisticated malware leverages accessibility permissions to gain control over calls, messages, and other sensitive data, tricking users into sharing critical financial information.
- FakeCall Malware Evolution: Initially targeting South Korea, this malware family has evolved with advanced vishing (voice phishing) capabilities to deceive users globally.
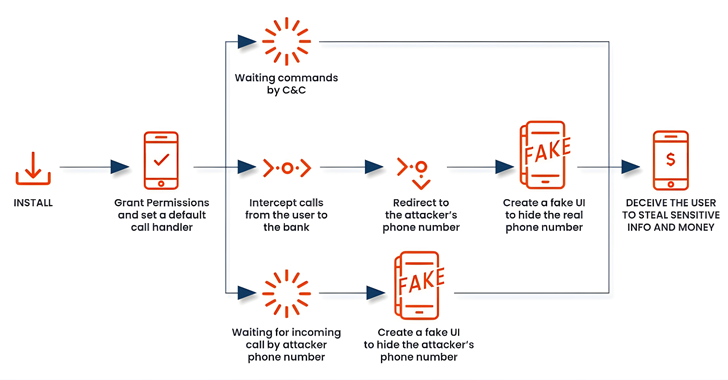
- Hijacked Calls: FakeCall can set itself as the device’s default dialer, intercepting and redirecting calls intended for banks to rogue numbers under attackers' control.
- Sophisticated Permissions Abuse: By exploiting accessibility services, FakeCall can perform actions such as taking pictures, recording audio, tracking location, and even imitating a live video feed.
- Convincing UI Imitation: The malware creates a fake UI resembling the legitimate Android call screen, misleading victims into believing they are speaking with their bank.
- Enhanced Espionage: FakeCall collects SMS messages, contacts, installed apps, and can delete or add contacts, making it a potent tool for data theft.
- Growing Mobile Phishing (Mishing): The malware’s approach showcases evolving mobile phishing tactics countering improved security measures and caller identification efforts.
FakeCall’s new variant highlights a critical need for mobile security vigilance, particularly for financial app users. Net Protector Mobile Security offers a proactive defense, including real-time protection and anti-phishing measures to block malicious apps, phishing links, and fraudulent calls.
Comment(s)