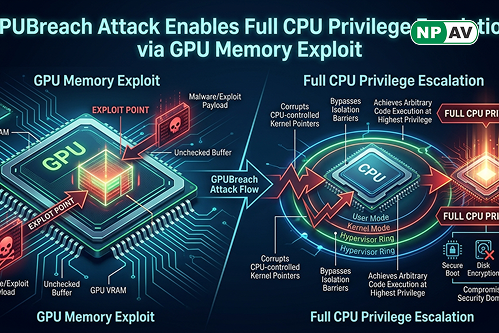
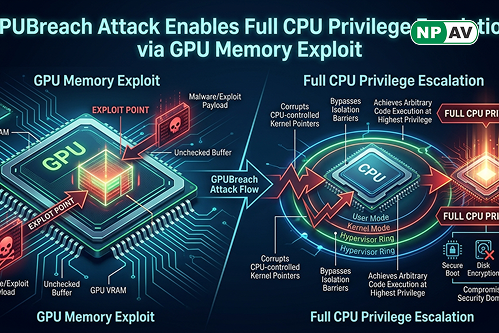
GPUBreach Attack Enables Full CPU Privilege Escalation via GPU Memory Exploit
Researchers have uncovered a new class of GPU-based attacks called GPUBreach, which can escalate privileges and potentially give attackers full control over a system. Building on the RowHammer vulnerability, the attack targets GDDR6 memory in high-performance GPUs to trigger bit-flips that corrupt critical memory structures, enabling unauthorized access.
Unlike earlier GPU attacks, GPUBreach can manipulate GPU page tables to gain arbitrary read/write access to memory and even escalate privileges to the CPU level. By exploiting weaknesses in NVIDIA drivers, attackers can bypass hardware protections like IOMMU and execute kernel-level actions, including spawning a root shell. Related techniques such as GDDRHammer and GeForge also demonstrate similar GPU memory exploitation capabilities.
This discovery raises serious concerns for cloud computing, AI infrastructure, and multi-tenant GPU environments. While enabling ECC memory may offer limited protection, researchers warn it is not foolproof. Currently, no complete mitigation exists for many consumer GPUs, making this a critical emerging threat in modern cybersecurity.
NPAV offers a robust solution to combat cyber fraud. Protect yourself with our top-tier security product, FraudProtector.net