Malware Alerts
-
Read moreExplore the intersection of celebrity culture and cybersecurity as we delve into the role of Pakistani actors in malware distribution. Discover insights, trends, and the implications for the entertainment industry.
-
Read moreA new phishing campaign in India exploits wedding invitations to distribute SpyMax RAT malware on Android devices. Learn how to recognize and protect yourself from this sophisticated cyber threat.
-
Read moreFBI warns of BADBOX 2.0 botnet infecting smart devices with pre-installed malware, enabling cybercriminals to hijack home networks and conduct illegal activity.
-
Read moreA sophisticated malware campaign is targeting WordPress and WooCommerce sites with obfuscated credit card skimmers and credential theft tools. Learn about the advanced techniques and implications of this growing e-commerce cyber threat.
-
Read moreThe NCSC has issued a warning about the UMBRELLA STAND malware targeting Fortinet FortiGate firewalls. Learn about its sophisticated techniques, persistence mechanisms, and the risks it poses to network infrastructure.
-
Posted: June 20, 2025Views: 135Read moreThe GodFather banking malware has evolved, utilizing on-device virtualization to hijack legitimate banking and cryptocurrency apps. Discover how this advanced threat operates and its implications for mobile security.
-
Posted: June 19, 2025Views: 89Read moreA new malware strain called SuperCard exploits hacked Android phones to steal payment card data during contactless transactions. Learn about its infection mechanism and the growing threat to mobile payment security.
-
Posted: June 17, 2025Views: 122Read moreA fraudulent loan app, "RapiPlata," has infected over 150,000 iOS and Android devices, stealing sensitive data and threatening users. Learn about the app's malicious tactics and ongoing risks.
-
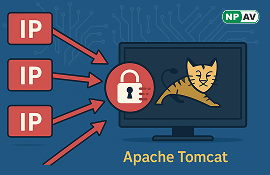
Read moreGreyNoise warns of coordinated brute-force attacks on Apache Tomcat Manager interfaces, involving 295 malicious IPs. Learn about the risks and recommended security measures.
-
Read moreA new malware campaign disguised as an Instagram growth tool is stealing login credentials. Learn how "imad213" works and how to protect your account.