Adware in Browser
Steps for Adware in Browser
Give the Adware PC to LAB or then take the logs as per below and add to Rcall ID
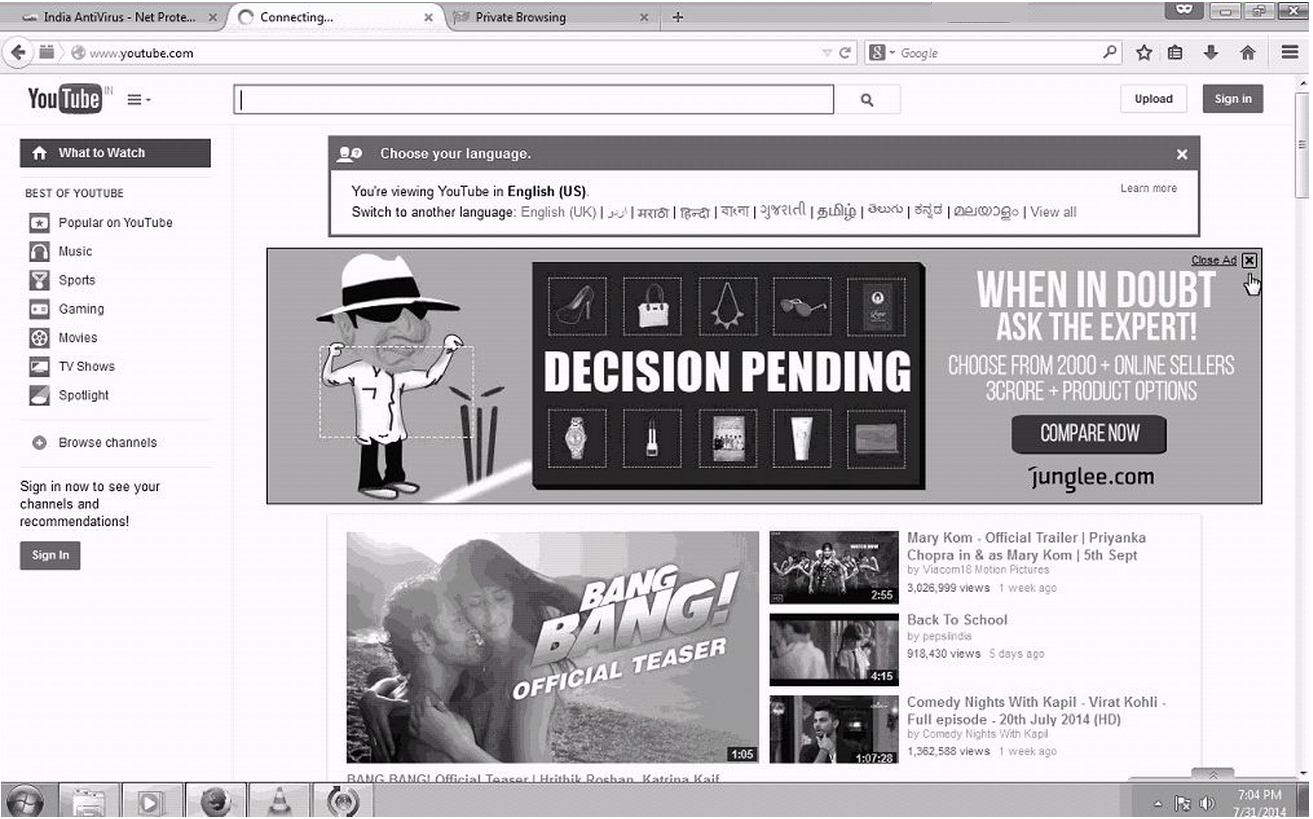
1. Take screen-shot of adware
2. Take screen-shot of extensions pages of browser
3. Run Mozillaext.exe
C:\Program Files (x86)\Net Protector 2014\EMAIL SCAN>MOZILLAEXT.EXE
Show in csv and take for both mozilla and chrome
4. Take Webprot Log
- Close all browsers
- Net Protector > Settings > Web Shield Tick Enable Web Shield and Tick Enable Log
- check task manager for webprot.exe service running
Service Name : Net Protector Web Prototection
exe name = C:\PROGRAM FILES (X86)\NET PROTECTOR 2014\Webprot.exe - Click on View Logs or folderC:\ProgramData\pcontrol\WebProtLog\date.logdelete or rename all old logs
- Now open www.corpwebcontrol.com or www.computermumbai.com web-site
and check for ads on these web-sites Refresh or F5 and wait for adsImp: Do not open any other web-site other that www.corpwebcontrol.com and www.computermumbai.com
- Take the webprot logs. the logs will have urls for adware
add the logs to manual report of rcall
6. Enable Net Protector > Protection Tab > "Advertise Blocker = ON"
7. Clear the browser cache, Disable Unwanted Extensions
Comment(s)






