GrassCall Malware Drains Crypto Wallets via Fake Job Interviews

A dangerous phishing campaign is targeting job seekers in the Web3 and cryptocurrency industry. Attackers are using fake job listings and fraudulent interview invites to trick victims into downloading a malicious video meeting app called GrassCall. Once installed, the malware steals login credentials, authentication data, and cryptocurrency wallets.
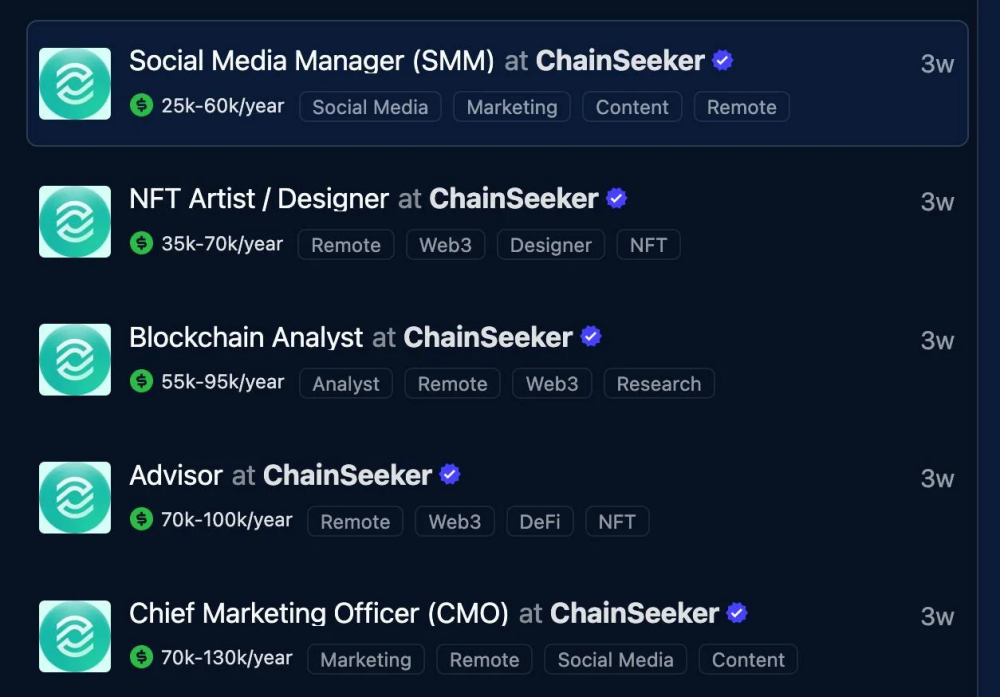
- Cybercriminals posted fraudulent job openings on LinkedIn, WellFound, and CryptoJobsList, posing as a company named ChainSeeker.io.
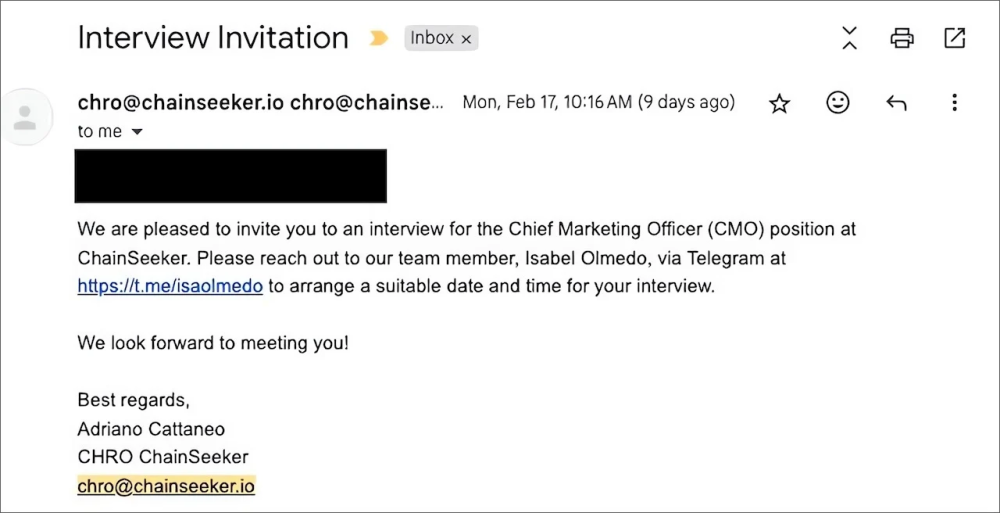
- Applicants received interview invites and were asked to connect with a fake Chief Marketing Officer (CMO) on Telegram to schedule the interview.
- Victims were tricked into downloading the GrassCall app from a fake website. The app installed information-stealing malware on both Windows and Mac devices.
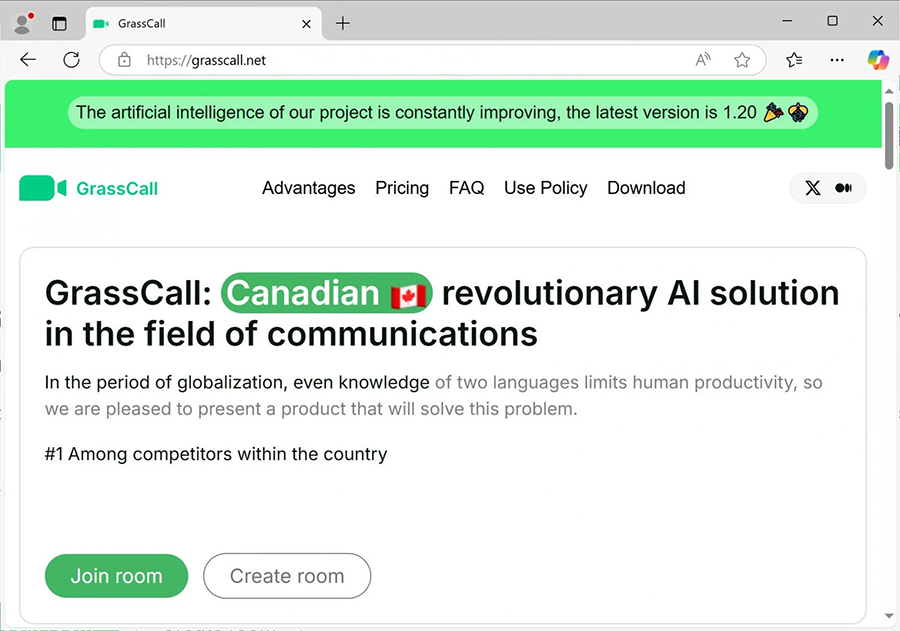
- On Windows, GrassCall installed Rhadamanthys infostealer and a Remote Access Trojan (RAT) to capture passwords and crypto wallets.
- On Mac, it deployed Atomic Stealer (AMOS) to extract stored credentials and sensitive information.
- Attackers uploaded stolen credentials to Telegram channels, where hackers paid for successful data breaches. Victims' crypto wallets were drained once hackers gained access.
- The fraudulent job postings were removed, and applicants were warned to scan their devices for malware.
Cybercriminals are constantly evolving their tactics to steal sensitive data and crypto assets. This GrassCall campaign highlights the growing risk of phishing attacks in the Web3 job market. Job seekers must remain vigilant, verify offers carefully, and follow strong cybersecurity practices to stay protected.
Stay alert, informed, and secure with Net Protector Cyber Security!
Comment(s)






