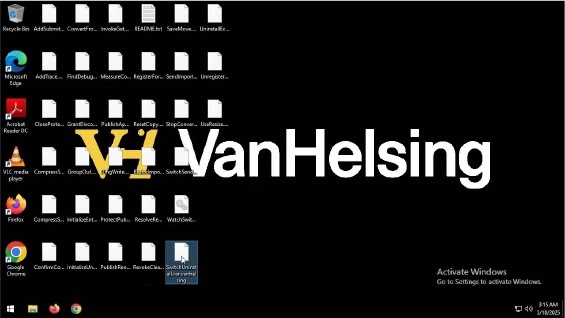
VanHelsing Ransomware Attacks Windows Systems With New Evasion Tactics

A new ransomware strain named VanHelsing is actively targeting Windows systems, using advanced encryption and evasion techniques to bypass security defenses. First discovered on March 16, 2025, this ransomware is particularly affecting government, manufacturing, and pharmaceutical industries in France and the United States.
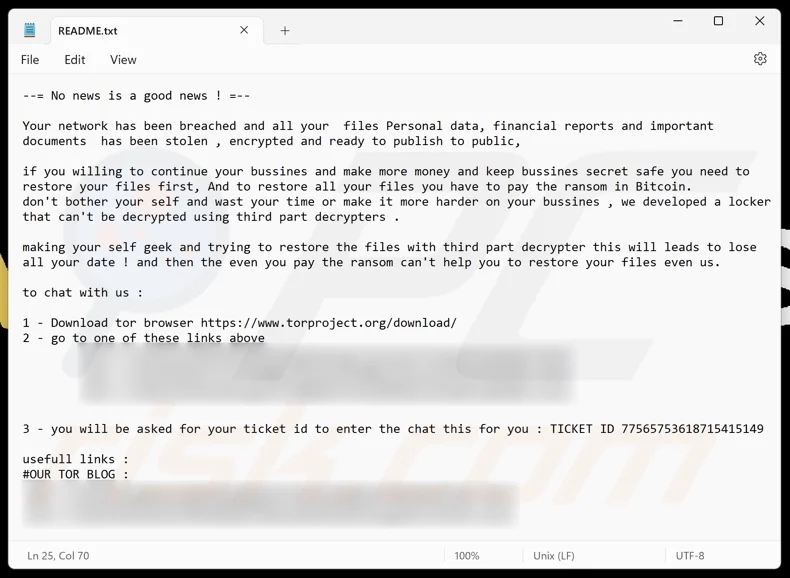
Once infected, victims see their files encrypted with the “.vanhelsing” extension, and a ransom note named “README.txt” is dropped on the system. The ransomware also changes the desktop wallpaper to display a message from the attackers.
- Double Extortion Tactics – Encrypts files and steals sensitive data (financial records, personal details, etc.) to pressure victims into paying the ransom.
- Sophisticated Evasion Techniques – Uses rootkits, direct volume access, process injection, and indicator removal to bypass detection by security solutions.
- Persistence Mechanisms – Modifies Windows registry settings, scheduled tasks, and system services to maintain access even after system reboots.
- Tor-Based Communication – Operates a dedicated chat portal on the dark web, allowing victims to negotiate with attackers.
- Credential Theft & Data Collection – Extracts sensitive system and email data, making recovery more difficult.
The rise of VanHelsing ransomware highlights the increasing sophistication of cyber threats in 2025. Businesses and individuals must remain vigilant, proactive, and well-prepared to prevent falling victim to such attacks. Investing in strong cybersecurity measures and maintaining good cyber hygiene is the key to staying protected.
Use Strong Endpoint Protection – Deploy advanced antivirus and endpoint detection tools like Net Protector Endpoint Security to detect and block ransomware threats.