Construction Industry Under Siege: Brute Force Attacks Target Foundation Accounting Software

Cybercriminals are intensifying efforts to breach corporate networks of construction firms by targeting exposed Foundation accounting servers. This particular software, extensively used within the construction industry, has become a prime target for hackers due to weak security measures on privileged accounts.
Attack Overview
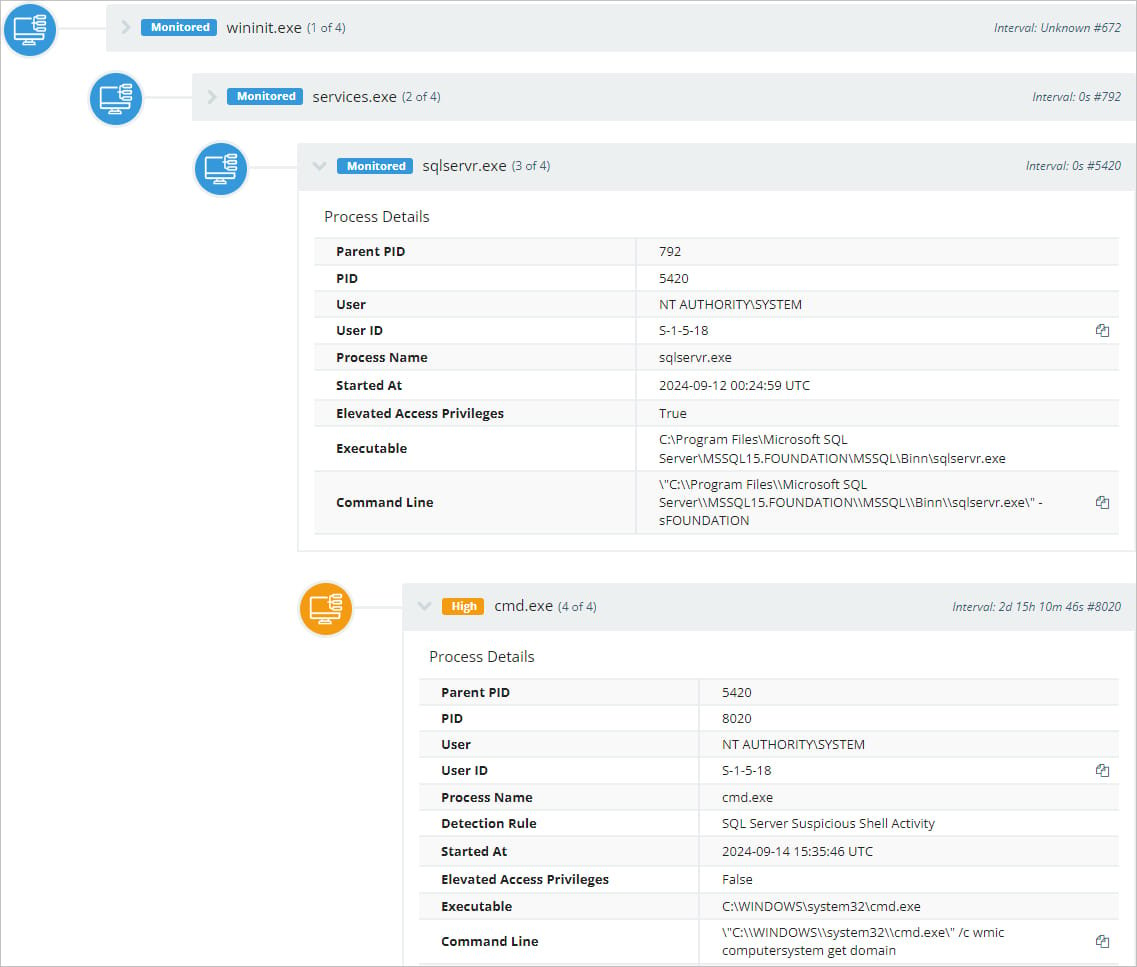
- Researchers from Huntress detected malicious activity on Foundation accounting software servers starting on September 14, 2024.
- Attackers are brute-forcing passwords on accounts with highly privileged access to exposed servers, specifically targeting plumbing, HVAC, concrete, and other construction sub-industries.
Open Ports and Weak Passwords
- The Microsoft SQL Server (MSSQL) used by Foundation is publicly exposed via TCP port 4243 to support a companion mobile app.
- Two default admin accounts, 'sa' and 'dba', are frequently targeted. Servers with default or weak passwords on these accounts are vulnerable to hijacking.
Aggressive Brute-Force Attacks
- Some servers experienced up to 35,000 brute force attempts per hour, overwhelming defenses and eventually cracking passwords.
- Once inside, attackers activate the xp_cmdshell feature, allowing them to run system commands like ‘ipconfig’ and ‘wmic’, collecting network and system data.
Widespread Impact
- Huntress monitored three million endpoints and identified 500 hosts running the vulnerable software, of which 33 publicly exposed MSSQL databases with default credentials.
- While the cloud-based version of Foundation remains secure, the on-premise variant has been the primary target of these attacks.
Defensive Measures
- Foundation Software has acknowledged the issue and recommended steps to mitigate the risks, advising users to rotate credentials and close unnecessary public ports.
- Huntress further recommends not exposing MSSQL servers unless necessary and to disable default accounts or enforce stronger password policies.
This attack serves as a stark reminder that strong password practices and secure configurations are critical in preventing breaches. Net Protector Cyber Security offers advanced solutions to safeguard organizations against such threats by hardening security and monitoring for brute force attempts across vulnerable systems.
Comment(s)
Categories
- Other (43)
- Ransomware (179)
- Events and News (28)
- Features (45)
- Security (505)
- Tips (83)
- Google (49)
- Achievements (13)
- Products (37)
- Activation (7)
- Dealers (1)
- Bank Phishing (61)
- Malware Alerts (299)
- Cyber Attack (383)
- Data Backup (15)
- Data Breach (232)
- Phishing (194)
- Securty Tips (9)
- Browser Hijack (30)
- Adware (15)
- Email And Password (90)
- Android Security (97)
- Knoweldgebase (37)
- Botnet (20)
- Updates (12)
- Alert (72)
- Hacking (90)
- Social Media (11)
- vulnerability (132)
- Hacker (107)
- Spyware (18)
- Windows (29)
- Microsoft (46)
- Uber (1)
- YouTube (4)
- Trojan (7)
- Website hacks (17)
- Paytm (1)
- Credit card scam (4)
- Telegram (9)
- RAT (12)
- Bug (5)
- Twitter (3)
- Facebook (14)
- Banking Trojan (17)
- Mozilla (2)
- COVID-19 (5)
- Instagram (5)
- NPAV Announcement (18)
- IoT Security (4)
- Deals and Offers (2)
- Cloud Security (12)
- Offers (5)
- Gaming (1)
- FireFox (2)
- LinkedIn (3)
- Amazon (5)
- DMart (1)
- Payment Risk (5)
- Occasion (3)
- firewall (5)
- Cloud malware (5)
- Cloud storage (2)
- Financial fraud (115)
- Impersonation phishing (4)
- DDoS (12)
- Smishing (2)
- Whale (0)
- Whale phishing (6)
- WINRAR (3)
- ZIP (2)
- Fraud Protector (101)
-
Mobile Frauds
(80)
- WhatsApp (21)
- AI (41)
Recent Posts






