.LUKITUS Ransomware - a new data locker!

.LUKITUS ransomware is very similar to the original Locky ransomware. It can enter your computer secretly via attachments of spam emails. 90% the victims were attacked by ransomware after opening malicious attachments of spam mails having a subject line related to online shopping or payment receipt.
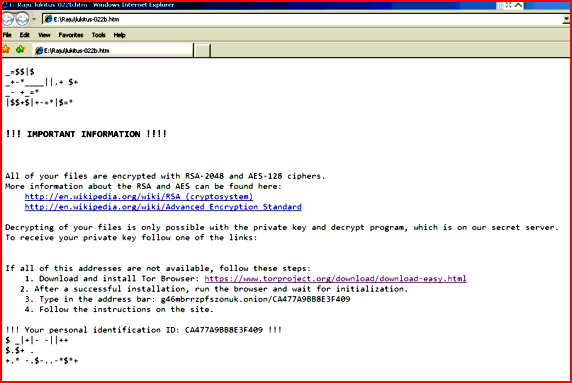
After infection, below screen will appear showing details about .LUKITUS ransomware encryption and payment.
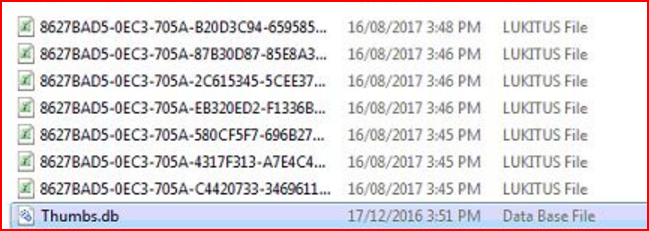
All your important files will be converted to LUKITUS file renamed with some random string. User will be unable to use these files.
Users are requested to follow below steps to secure your important data:
- Install and keep NPAV updated up-to-date.
- Make sure NPAV data backup is ON.
- Never use weak passwords on your accounts, especially on remote system access software.
- Do not click on unknown links while browsing the web and do not open emails sent by unknown people.
1 Comment(s)
Reshma W
Sep 02, 2017 20:36
thanks