New Android Spyware Locks Victims Out - Requires Password for Uninstallation

Cybersecurity researchers have discovered a dangerous new Android spyware app that uses password protection and Android overlay tricks to stay hidden and prevent uninstallation. Installed by someone with physical access, this app secretly spies on the victim while making it very hard to remove.
- Password-Protected Spyware: Spyware asks for a password during uninstallation, which only the installer knows — effectively locking the victim out from removing it.
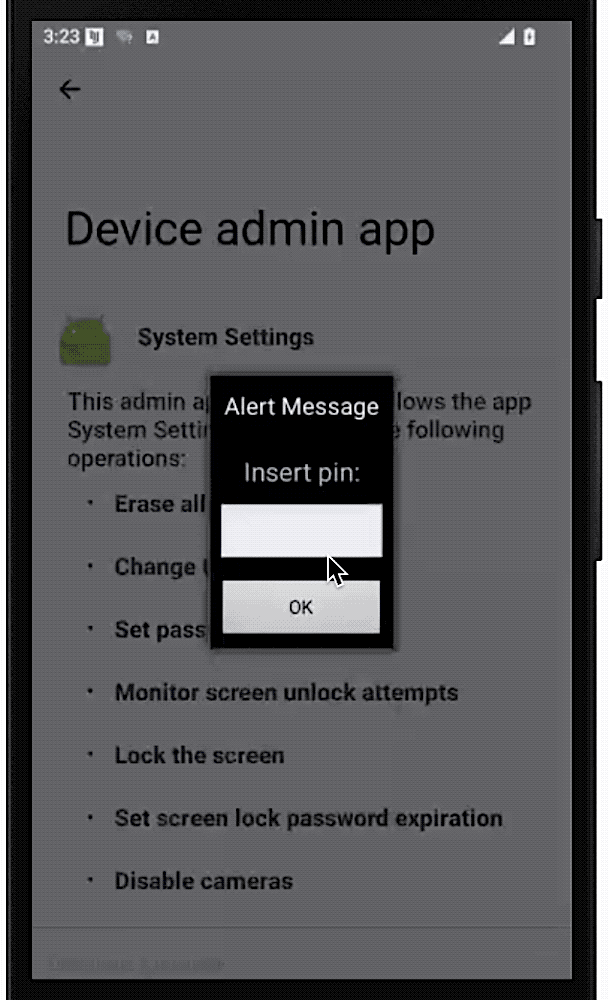
- Exploits Android Overlay: It uses Android’s legitimate "overlay" feature to display a fake password screen on top of settings, blocking any removal attempt.
- Gains Admin Access: Once installed, the app gives itself device administrator privileges and hides its icon, staying invisible on the home screen.
- Monitors Sensitive Data: Spyware can track messages, photos, GPS location, and more — turning the victim's phone into a spying device.
- Installed Manually: This spyware usually requires someone to have physical access to the phone and the screen unlock code to install it.
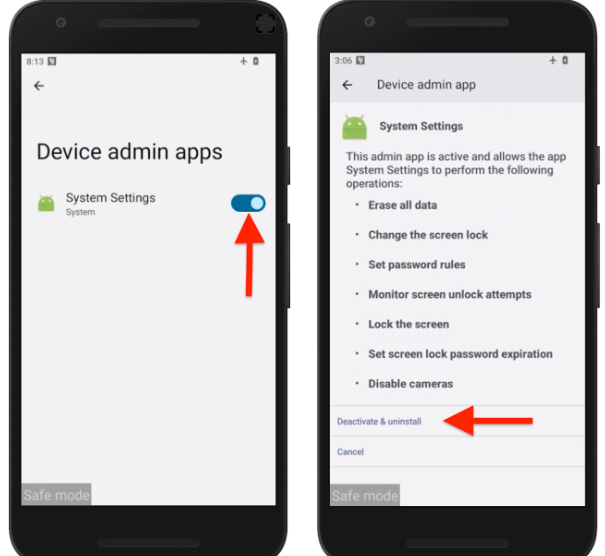
- Safe Mode Removal Trick: Thankfully, users can remove the app by booting the phone into Safe Mode, disabling device admin access, and then uninstalling it.
To Stay Protected:
- Keep Google Play Protect enabled.
- Regularly check device admin apps in your settings.
- Avoid leaving your phone unattended or unlocked.
- Use a trusted antivirus like Net Protector Mobile Security to detect and remove spyware.
- Watch out for unusual behavior like overheating, fast battery drain, or increased data usage.
This spyware is a serious warning about how even basic Android features can be abused to trap users. While it’s often disguised as a tool for parental or employee monitoring, it can easily become a weapon for stalking and spying.
Net Protector Cyber Security advises all Android users to stay alert, protect their devices with reliable security software, and take action at the first sign of suspicious activity.
Comment(s)