Oracle Gen 1 Servers Breached - Millions of Records Compromised by Cyberattack

Oracle has confirmed a major data breach targeting its older Gen 1 servers, exposing sensitive authentication data, usernames, and hashed passwords. The attacker gained access using an old Java exploit and demanded a $20 million ransom.
Breach Confirmed by Oracle
Oracle acknowledged that its Gen 1 cloud infrastructure was compromised, with data reportedly stolen from around 6 million records.
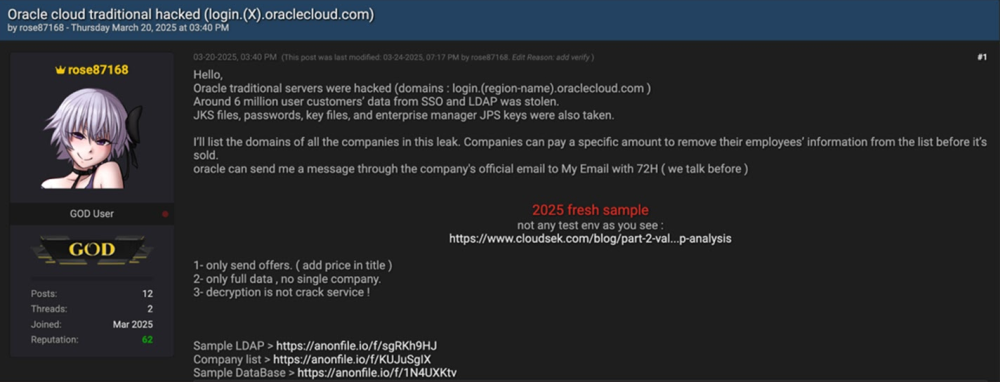
Threat Actor "rose87168" Claims Responsibility
A hacker named “rose87168” disclosed the breach on BreachForums and is demanding a $20 million ransom, while also offering the data in exchange for zero-day exploits.
What Was Stolen?
- Usernames and email addresses
- Hashed passwords
- Sensitive SSO and LDAP credentials
- Java Key Store (JKS) files
- Enterprise Manager JPS keys
How Did the Attack Happen?
The attacker used a 2020 Java vulnerability to implant a web shell and malware targeting Oracle’s Identity Manager (IDM) systems.
Access was likely gained in January 2025, but Oracle only detected the breach in late February.
Old Systems, New Threats
Oracle confirmed the stolen data is around 16 months old and only affected Gen 1 servers, not the newer Gen 2 infrastructure.
Oracle’s Response
- Notifying affected clients
- Strengthening security around legacy servers
- Ensuring Gen 2 systems are safe
- Denying any breach of core Oracle Cloud infrastructure
A Growing Pattern of Attacks
This breach comes just weeks after another incident involving Oracle Health’s legacy Cerner systems — raising concerns about Oracle’s security posture for older platforms.
This attack is a strong reminder that legacy systems remain a weak point in many organizations' cybersecurity. Even global tech giants like Oracle aren’t immune to exploits rooted in outdated software. It’s crucial for all businesses to regularly patch, upgrade, and migrate from older platforms to avoid similar breaches.
Stay alert. Stay updated. Stay protected — with Net Protector Cyber Security.






