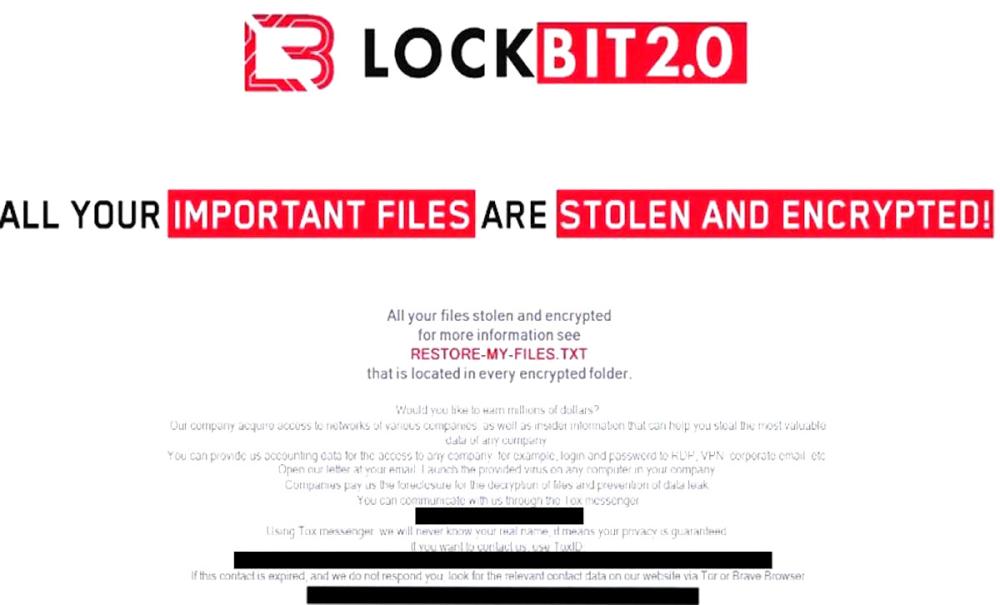
Ransomware Gangs Impersonate LockBit to Intimidate Victims and Leverage AWS in Latest Attacks

Ransomware gangs are using the notorious LockBit’s reputation to intimidate victims and carry out sophisticated data exfiltration attacks via Amazon S3 Transfer Acceleration. These attacks exploit embedded AWS credentials and target Windows and macOS systems, encrypting data and applying pressure tactics to extract ransom payments.
- Threat actors impersonate LockBit ransomware to increase pressure on victims.
- Attackers abuse Amazon S3 Transfer Acceleration for faster data exfiltration.
- Embedded AWS credentials used for cloud storage in ransomware attacks.
- Over 30 ransomware samples detected targeting both Windows and macOS systems.
- Files encrypted and renamed with initialization vectors in the format: <filename>.<initialization vector>.abcd.
- Attackers display LockBit 2.0 images as ransom notes to coerce payments.
- The rise of cross-platform ransomware showcases evolving tactics in the cyber threat landscape.
- Notable vulnerabilities exploited in recent ransomware campaigns include CVE-2020-3259, CVE-2023-20269, and CVE-2024-40766.
- Akira, a ransomware group, leverages a Rust variant to target organizations in critical sectors.
- Microsoft’s analysis shows a 2.75x increase in ransomware-linked encounters from 2023 to 2024.
Ransomware gangs continue to evolve, adopting sophisticated methods like leveraging cloud services and impersonating notorious ransomware groups like LockBit. This adds extra pressure on victims while facilitating rapid data theft and encryption across platforms. The increasing use of AWS services highlights a dangerous trend in the weaponization of cloud infrastructure for cybercrime.
Comment(s)