Npav Lab
-
Read moreA critical SolarWinds Web Help Desk vulnerability (CVE-2025-26399) allows attackers to execute commands via deserialization flaws. CISA warns organizations to patch immediately.
-
Read moreInstagram experienced a major outage on March 11, 2026, leaving thousands of users unable to access feeds, post content, or send direct messages worldwide.
-
Read moreA powerful iPhone exploit toolkit called Coruna, originally built by a U.S. defense contractor, has leaked and is now used by Russian spies and cybercriminals to target iOS devices.
-
Read moreCognizant’s TriZetto Provider Solutions disclosed a major data breach exposing sensitive health information of 3.4 million patients after attackers accessed external systems.
-
Read moreResearchers warn that indirect prompt injection attacks allow hackers to manipulate AI agents using hidden instructions in web pages, enabling phishing, data theft, and system compromise.
-
Read moreA new phishing campaign targeting LastPass users uses fake support emails, display name spoofing, and fraudulent login pages to steal vault master passwords.
-
Read moreSilver Dragon, a threat group linked to APT41, is targeting government entities using Cobalt Strike, DLL sideloading, DNS tunneling, and Google Drive-based command-and-control techniques.
-
Posted: February 04, 2026Views: 406Read moreFake India Post GDS recruitment websites are stealing user data. Learn how to identify phishing sites and stay protected with NPAV security.
-
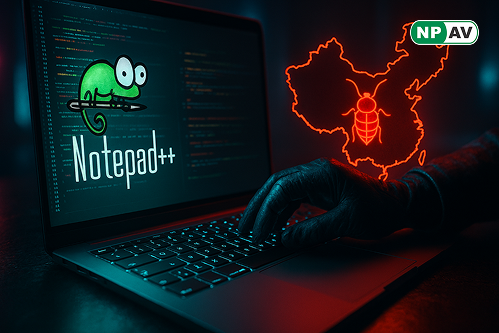
Read moreChina-linked Lotus Blossom group breached Notepad++ hosting, delivering Chrysalis backdoor via tampered updates. Learn the attack details and how to stay safe.
-
Read moreCelebrate Republic Day 2026 by securing your online life with Total Security Fraud Protector. Protect banking, emails, passwords, and personal data from cyber threats and fraud.