NPAV End Point Security launched the "Hardware Tracking and Inventory Management" Feature

Hardware Inventory Management:
This is very useful feature to manage network PC's assets for small and big organization. It shows/export full hardware inventory report groupwise over the LAN. System admin can add notes/details to selected PC for further reminder.
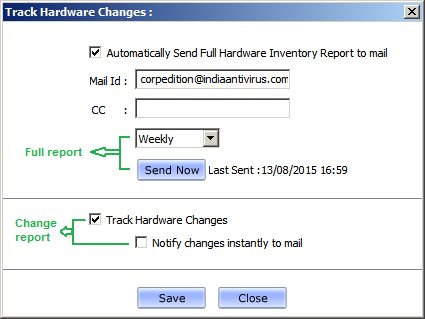
Hardware Tracking Mail:
The End Point Security helps to track the entire network PC's assets very easily. The system administrator can get the hardware change components information on End Point Security server PC.
Report Types:
1. Change Report : Get the instant change report over the mail also it can be send to Cc mail ID.
2. Full Report : Administrator can get the full inventory report by clicking on "Send Now" button or automatically with specified interval.
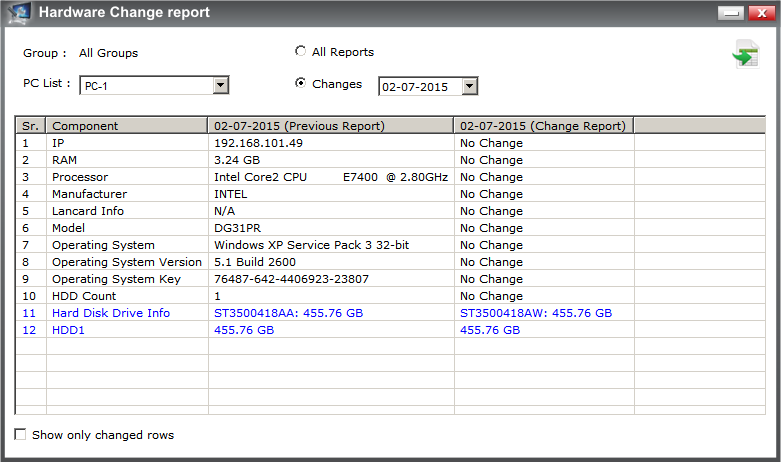
Show Hardware Changes:
This will list the changed hardware components with respect to change date.Admin can export the change report to CSV. Admin can see report of any PC from selected group.