Npav Lab
-
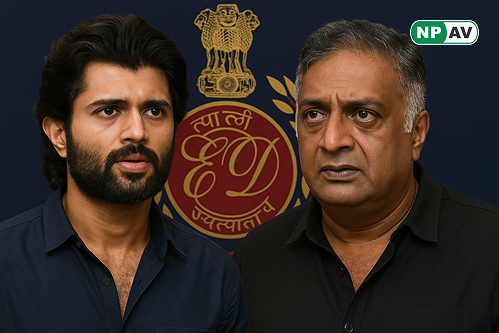
Read moreThe Enforcement Directorate investigates a betting app scam involving Tollywood stars like Vijay Deverakonda and Prakash Raj. Learn about the allegations, celebrity responses, and the legal implications of this high-profile case.
-
Read moreDiscover how India's Enforcement Directorate uncovered a ₹284 crore illegal betting operation linked to the "opinion trading" app Probo. Learn about the deceptive practices and foreign funding involved in this major crackdown on online gambling.
-
Read moreExplore the tragic case of Raj Leela More, a chartered accountant who took his own life after being blackmailed for ₹3 crore by individuals he met on Instagram. Learn about the emotional and financial toll of online manipulation and extortion.
-
Read moreDiscover how a new Trojan malware, developed using reinforcement learning, can consistently bypass Microsoft Defender for Endpoint. Learn about its implications for cybersecurity and the advancements in AI-driven malware development.
-
Read moreLearn about SparkKitty, a sophisticated Trojan malware targeting iOS and Android devices to steal personal photos. Discover its distribution methods and the risks it poses, particularly in Southeast Asia and China.
-
Read moreDiscover how the Anatsa banking trojan infected 90,000 users through a fake PDF app on Google Play. Learn about the tactics used by cybercriminals and how the malware operates to steal banking credentials.
-
Read moreA Bengaluru pharmaceutical company lost ₹1.9 crore (US$230,000) to cyber scammers impersonating the chairman. Learn how the fraud unfolded and the tactics used by cybercriminals in this sophisticated spoofing attack.
-
Read moreDiscover how organized scams are exploiting the IRCTC system for Tatkal train tickets. Learn about the tactics used by fraudsters and the measures taken by the Ministry of Railways to protect genuine travelers.
-
Posted: July 08, 2025Views: 239Read moreLearn how to spot and avoid traffic e-challan scams that involve fake violation notices and malicious payment links. Discover essential tips to protect yourself from fraudsters and verify your e-challan details safely.
-
Read moreA chartered accountant, Abhishek Agarwal, was arrested by the Uttarakhand STF for orchestrating a ₹750 crore cybercrime operation involving fraudulent loan apps linked to Chinese nationals. Discover the details of the investigation and the implications of this scam.